
How could a PUP be unwanted? Well, in this case, we are not referring to a fluffy, playful dog or even Power Pup the Office Assistant. We’re referring to a term that is increasingly being used to describe Potentially Unwanted Programs. We are likely all too familiar with a virus infection; your PC becomes infected when opening something such as an email attachment or having something downloaded without your consent when visiting an infected website – even ones that are considered legitimate can be sabotaged. A PUP on the other hand can be installed with your consent – even though you may not know it.
Let’s Get Started!
We’re going to look at a general definition and description of these two types of PC predicaments.
Virus
A virus is a type of malware (malicious software program), that is installed on your system without consent and will replicate itself in whole or in part. It behaves in a manner that can be thought of as an infection by targeting one or more areas of your PC. You can often expect to experience harmful activities or negative impacts such as monopolizing system resources (disk space and CPU), gaining access to private data, sending out spam content, corrupting data on the system, and displaying messages on the screen (popups). While these harmful behaviours are typically expected not all viruses come equipped with a damaging payload.
Other traits:
- Creators of viruses exploit security vulnerabilities on your system and are motivated by profit, desire to spread messages, sabotage, or operate for personal pleasure and sense of mastery.
- Computer viruses cause billions of dollars worth of damage each year.[2]
- Most viruses target computers running Microsoft Windows operating systems and often using complex stealth and anti-detection strategies to evade anti-virus programs. As we point out in upcoming sections, Windows offers free tools to prevent and cure issues as a result of viruses.
PUP
This term, short for Potentially Unwanted Program, refers to items that may be unwanted. This can include spyware (tracking software that gathers information), adware (where advertisements are displayed during operation), and dialers (if you have a modem, a dialer can make pay-per-call phone calls to other computers). Most frequently it includes items you downloaded but without explicit consent. In other words, you said yes but didn’t read the fine print. One or more PUPs are most often downloaded along with software that you did in fact want (bundled together). These items can bog down your system and can cause poor PC performance.
In a previous article we introduced “foistware” – a term derived from the word “foist” which is to foist upon or impose fraudulently or unjustifiably as with inferior merchandise on a customer. This includes software that gets installed in addition to software you intended to install without your full knowledge or through stealthy methods such as being bundled with software you actually want. The result can take the form of:
- Additional Internet browser toolbar add-ons,
- Changes to your default search engine (for example, from Google search to Bing),
- Changes to your browser homepage,
- Display of pop-ups with scary messages like “Back up your PC or lose it”, or “Your computer has 1000 errors”.
Unlike a virus, a PUP does not have the ability to replicate itself. As for “unwanted”, they can include behaviours that result in negative impacts such as popups and annoying messages appearing and resources being excessively utilized (hard drive space or CPU).
Software vendors use bundling techniques frequently when offering a free application. We have mentioned in previous articles how “free” is not always free; this is yet another example. This is yet another example. To gain revenue a software vendor will partner with a less desirable software creator to deliver a bundled program that requires you to carefully select what you are installing during the install process as we soon point out. Once on your system, the manufactures of the less desired software provide advertisement or benefit from you clicking to their site.
These types of unwanted programs are not technically malware but have undesirable side effects for your PC as listed above. Side effects can also include slower performance as these items will launch processes that run in the background.
Treatments:
There are ways of treating these PC plights. However, as can be expected there is not one solution that works in all instances. You cannot expect anti-virus tools to work for items that have been installed to your system with your consent albeit using dodgy methods. We are going to reverse the order here and start with what should be easier to deal with –potentially unwanted programs. If you cannot deal with them using these methods… chances are you are dealing with something more malicious.
Remove PUP
The process of removing a PUP is to begin by identifying it. With PC Clean Maestro you can use the Uninstaller tool. Begin by opening the program and following these steps:
- Click the Uninstaller button in the left navigation bar.
- The Uninstaller tool will appear and a complete list of programs is displayed as seen here:
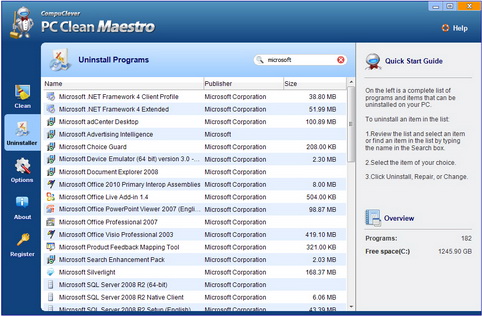
- Review the list by selecting any item and use the Program Information in the right pane to help identify programs.
- If there are items you do not know and you are unsure if you should remove the item go online to better verify it. You can enter the program name in the Should I Remove It website. This site provides removal percentages and ratings for a wide range of programs.
- Return back to PC Clean Maestro when making your decision and uninstall the item if you are certain you do not need it using the Uninstall button.
Clean Virus
There are free anti-virus tools that have been developed and there are pay-to-use solutions that are part of a multi-billion dollar industry. Unfortunately, no one software program can provide 100% protection and offer the ability to remove all types of viruses as there are countless known viruses and new ones constantly being introduced. New viruses that appear take time for the creators of anti-virus programs to include in their arsenal of protection. This is why constant updating of these kinds of programs is required. Fortunately free tools are open source; that is, free and open for anyone to run, modify and update so as to be available to the public domain.
Tools include:
- Malicious Software Removal Tool (MSRT): It supports XP, Vista, Windows 7, and Windows 8.
- Windows Defender – provides always-on, real-time protection against spyware, adware, keyloggers, and so on. It supports XP, Vista, and Windows 7.
- Microsoft Security Essentials – and all-in-one, consumer-security tool to detects and removes a wide range of malware. It supports XP, Vista, and Windows 7.
- Win8 Defender – provides the same level of protection against malware as Microsoft Security Essentials but for Windows 8.
- Microsoft Safety Scanner – for detecting malware hidden at even the deepest levels of your system. It supports XP, Vista, Windows 7, and Windows 8.
- Windows Defender Offline (WDO) – Microsoft’s most powerful anti-malware tool for consumers.
Our recommendation to average consumers:
- For Windows XP, Vista, and Windows 7 users: Microsoft Security Essentials.
- For Windows 8 users: Windows 8 Defender.
Detection and Prevention:
To prevent a PUP from being downloaded to your system you need to be very vigilant when downloading anything. This means you need to detect when a program is bundled with other add-ons during the installation process. When installing software you typically see a step-by-step install wizard that guides you through the process and offers you choices along the way. The choices you make – even during the EULA (End User License Agreement) – will determine what you accept to be downloaded.
We recommend that you follow this link for a very clear, step-by-step example of potentially unwanted programs and how you can detect and avoid downloading these unwanted apps.
In Summary:
Even when software is installed to your system using legitimate means there are instances when additional software and add-ons, sometimes referred to as “crapware”, are included. What you get isn’t what you see. Removal can be questionable when you don’t know what you are dealing with. With the information provided here you now have the tools and knowledge to better identify these and to remove them.
We hope this article has helped gain some insight and offered you some effective strategies on cleaning your PC. We will continue to provide story lines like this that benefit all of us and we will describe them in a manner that is within reach of everyday computer users. If you have some ideas of topics you would like us to cover, email us at: newsletter@compuclever.com
